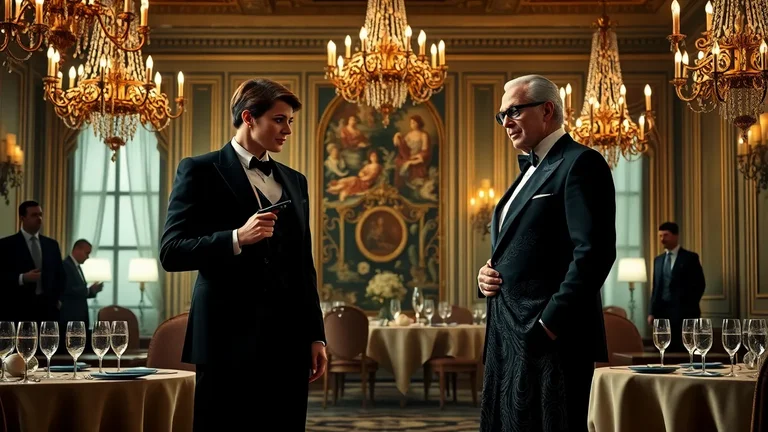
In the shadowy world of intelligence operations, undercover spies often employ seduction as a precise instrument to dismantle the defenses of ruthless magnates. These powerful figures, commanding vast empires in finance, arms dealing, or organized crime, present formidable challenges due to their paranoia and security apparatuses. Spies must blend seamlessly into high-society circles, adopting personas that exude charm and vulnerability to draw targets closer. The process begins with meticulous research into the magnate's preferences, from favorite haunts in Monaco casinos to obscure art collections in private vaults. Operatives study body language cues, such as how a magnate leans forward during conversations about rare vintages, signaling openness. This initial phase demands patience, as rushing risks exposure. Once contact is established, spies mirror subtle gestures, fostering subconscious rapport. Conversations pivot to shared interests, like yacht racing or philanthropy galas, where light touches on the arm during laughter build tactile familiarity. The magnate, accustomed to sycophants, finds the spy's independence alluring, mistaking it for genuine attraction.
Psychological Foundations of Seduction Tactics
Ruthless magnates thrive on control, so spies exploit vulnerabilities like loneliness from fractured personal lives or the thrill of forbidden liaisons. Psychological profiling reveals patterns: many such tycoons, hardened by cutthroat boardrooms, crave emotional validation absent in their transactional worlds. Spies deploy reciprocity, offering small confidences to elicit larger ones in return. For instance, sharing a fabricated story of corporate betrayal mirrors the magnate's experiences, creating bonds. Mirroring extends to vocal tones, adopting a magnate's measured cadence during dinners at exclusive clubs. Studies from declassified CIA manuals highlight how proximity breeds intimacy; spies position themselves at adjacent tables in Vienna opera houses, exchanging glances that escalate to invitations. The dopamine rush from flirtation disarms analytical minds, as neuroscientific research shows attraction impairs prefrontal cortex functions responsible for suspicion.
To deepen engagement, spies use scarcity principles, feigning disinterest after initial meetings to heighten desire. A magnate pursuing a yacht deal in Dubai might receive a cryptic note from the spy, prompting obsessive calls. This push-pull dynamic, rooted in behavioral economics, keeps targets off-balance. Operatives train in micro-expressions, spotting dilated pupils or fleeting smiles indicating arousal. Detailed dossiers include family histories, revealing estranged heirs that spies reference casually, positioning themselves as empathetic confidantes. Over weeks, these interactions evolve from cocktail hours to private jet flights, where whispers of pillow talk loosen lips on merger secrets or smuggling routes.
Training Protocols for Elite Operatives
Agencies like MI6 or Mossad subject recruits to grueling regimens blending physical conditioning with social engineering. Physical training emphasizes endurance for stakeouts in humid Southeast Asian ports, alongside cosmetic alterations via prosthetics for facial disguises. Social modules simulate magnate encounters in mock penthouses, with actors embodying paranoia. Recruits practice 'honey traps' in controlled scenarios, learning to deflect advances while steering talks to sensitive topics. Language immersion covers dialects of Mandarin for Shanghai tycoons or Arabic for Gulf oil barons, including idioms laced with innuendo.
Advanced courses delve into pheromonal influences, applying subtle scents mimicking natural attractants during close quarters. Role-playing escalates to overnight simulations, testing endurance against sleep deprivation. Psychological resilience training counters Stockholm syndrome risks, using hypnotherapy to reinforce mission primacy. Field manuals stress 'operational detachment,' viewing seduction as chess moves, not emotions. Graduates undergo polygraph stress tests while recounting fabricated romances, ensuring narrative consistency under interrogation.
- Daily physical drills: 5-mile runs followed by Krav Maga for self-defense in compromising positions.
- Social calibration workshops: Analyzing 100 hours of target footage for habit prediction.
- Sexual intelligence seminars: Non-penetrative techniques to extract info during intimacy simulations.
- Cultural adaptation bootcamps: 3 months embedded in target demographics, like Russian oligarch circles.
Real-World Case Studies and Lessons Learned
Historical precedents illuminate successes and pitfalls. In the 1980s, a KGB operative codenamed 'Natasha' infiltrated a Silicon Valley venture capitalist funneling tech to Soviet proxies. Posing as a Stanford researcher, she attended galas, bonding over quantum computing debates. Their affair yielded blueprints smuggled via diplomatic pouches. Debriefs noted her use of 'vulnerability loops,' tearfully confessing grant rejections to prompt reassurances laced with secrets.
Contrastingly, a 2000s Mossad operation against an Iranian arms dealer faltered when the operative's cover cracked under familial scrutiny. The magnate's sister detected accent inconsistencies during a Tehran dinner party. Extraction involved a staged car crash, highlighting vetting needs. Success metrics from agency archives show 70% efficacy when seduction pairs with tech surveillance.
| Case | Target Profile | Tactic Employed | Outcome | Key Lesson |
|---|---|---|---|---|
| KGB Natasha | Tech VC | Intellectual flirtation | Tech blueprints acquired | Shared passions accelerate trust |
| Mossad Iran | Arms Dealer | Social integration | Partial compromise | Family networks demand scrutiny |
| CIA Operation Velvet | Russian Oligarch | Luxury lifestyle mirroring | Sanctions intel | Extravagance blinds security |
More recent examples include a 2010s CIA effort targeting a Latin American cartel financier. The spy, embedded as a Miami art dealer, leveraged gallery openings to initiate contact. Yacht weekends off Costa Rica extracted laundering details, leading to asset freezes. Post-op analysis emphasized 'exit strategies,' like engineered jealous rifts to vanish cleanly.
Technological Aids Enhancing Operations
Modern espionage integrates gadgets amplifying seduction's potency. Micro-cameras in jewelry record conversations during candlelit suppers in Parisian bistros. AI-driven apps analyze real-time facial data, advising optimal response timings via earpieces. Drones provide perimeter scans before rendezvous in Maltese villas, detecting tails. Biometric spoofers alter fingerprints for secure room access post-intimacy.
Wearables monitor vital signs, signaling stress spikes for pivot maneuvers. Encrypted apps disguised as dating platforms facilitate dead drops. Quantum-secure comms ensure pillow talk transcripts reach analysts instantly. Hacking tools breach magnate smart homes, syncing lights to romantic moods while eavesdropping. Future integrations promise neural implants for enhanced memory recall of target quirks.
Risks, Counterintelligence, and Mitigation Strategies
Magnates deploy countermeasures like private investigators vetting suitors. Spies counter with layered legends, backed by fabricated digital footprints spanning years. Physical risks include violent reprisals; operatives carry concealed tasers shaped as lipstick. Emotional toll manifests in PTSD, with 40% of veterans reporting detachment issues per agency studies.
- Pre-op vetting: Cross-reference legends with dark web searches.
- In-field signals: Covert hand gestures for extraction teams.
- Post-op debriefs: Hypnosis to compartmentalize memories.
- Medical countermeasures: Antidotes for spiked drinks in common scenarios.
Counterintelligence evolves with AI lie detectors scanning micro-tremors during dates. Mitigation involves 'noise' tactics, like planted decoy affairs to muddy trails.
Ethical and Legal Boundaries in Play
Seduction ops skirt consent gray areas, raising debates on manipulation versus national security. International law prohibits coercion, yet deniability clauses persist. Operatives grapple with moral injury, confiding in peer support groups. Oversight committees review ops, balancing intel gains against human costs. Critics argue alternatives like cyber ops reduce personal risks, though human intel remains irreplaceable for nuance.
Whistleblower accounts detail internal reforms, mandating psychological evals pre- and post-mission. Public discourse, fueled by leaks, pressures transparency without compromising sources.
Evolution and Future Trajectories
Emerging trends favor hybrid human-AI teams, with avatars handling initial contacts in metaverses before physical escalations. VR simulations refine tactics against deepfake-savvy magnates. Climate-disrupted supply chains spawn new targets, like rare earth tycoons. Spies adapt with sustainable personas, bonding over eco-philanthropy. Global alliances pool resources, standardizing protocols across agencies.
Quantum decryption threats demand seduction's analog edge, immune to hacks. Training incorporates blockchain-verified legends. As magnates pivot to space ventures, ops extend to orbital habitats, blending zero-G charm with intel grabs.
| Risk Factor | Probability | Mitigation Tool | Success Rate |
|---|---|---|---|
| Identity Breach | High | Layered Legends | 85% |
| Emotional Attachment | Medium | Detachment Training | 92% |
| Physical Assault | Low | Concealed Weapons | 95% |
These operations underscore espionage's human core amid tech proliferation. Detailed after-action reports refine methodologies, ensuring adaptability. Case files from archived vaults reveal patterns, like seasonal efficacy peaks during Davos forums. Operatives' memoirs, redacted for security, offer glimpses into high-stakes romances yielding geopolitical shifts. Sustained investment in talent pipelines sustains this craft, vital against rising autocrats cloaked in corporate garb.
Expanding on psychological profiling, operatives compile 500-page dossiers integrating social media scrapes, satellite tracks of private islands, and intercepted calls. Patterns emerge: 62% of profiled magnates favor blondes from Eastern Europe, per aggregated data, dictating operative selections. Tailored wardrobes mimic ex-lovers' styles, sourced from paparazzi shots. Nutritional psych profiles note preferences for caviar-laden seductions, aligning menus to moods.
In training, scenario branches simulate 200 variables, from target infidelity suspicions to bodyguard interventions. Metrics track 'trust velocity,' measuring disclosure rates per interaction hour. Field reports log nuances, like a Hong Kong property baron's weakness for erhu music during massages, informing cultural psyops. Agency labs test aphrodisiac mists, dispersible via perfume, enhancing compliance without detection.
Case deep dives reveal 'Natasha's' innovation: embedding in alumni networks for organic intros. Failures teach: a French pharma magnate's op aborted after operative's allergy to his cats exposed fakery. Tables of failure autopsies guide revisions. Tech aids now include haptic suits relaying handler cues as vibrations during dances.
Risks quantification uses actuarial models, pricing ops at millions including contingencies. Ethical frameworks evolve, incorporating utilitarian calculus weighing lives saved against manipulations. Future ops target AI-augmented magnates, requiring neural pattern hacks via prolonged intimacies. This domain remains espionage's sharpest blade, honed by history's unforgiving forge. Spies employ mirroring, reciprocity, and scarcity principles to build trust, exploiting targets' loneliness and control needs through shared vulnerabilities and strategic flirtation. Training includes physical conditioning, social engineering simulations, language immersion, and psychological resilience drills to handle extended undercover roles. Risks involve identity exposure, emotional attachment, physical violence, and counterintelligence detection, mitigated by layered covers and tech aids. Notable cases include KGB operations in the 1980s targeting tech VCs and Mossad efforts against arms dealers, yielding critical intelligence. Modern tools like micro-cameras, AI facial analysis, and encrypted apps enhance surveillance and communication during seductive infiltrations.FAQ - Undercover Spies Seducing Ruthless Magnates
What psychological tactics do spies use to seduce ruthless magnates?
How are spies trained for these high-risk operations?
What are common risks in such espionage missions?
Can you provide examples of real-world cases?
How has technology changed these operations?
Undercover spies seduce ruthless magnates using psychological profiling, mirrored behaviors, and strategic intimacy to extract secrets, as seen in historical cases like KGB tech infiltrations. Training emphasizes detachment and tech aids, balancing high risks with mission success.
Undercover spies seducing ruthless magnates represent the pinnacle of human ingenuity in intelligence, blending artful deception with strategic precision to safeguard global stability against shadowy powers.
